Cyber Security 101: Common Types of Malware
Cyber security is one of the constant issues that worries small to medium businesses in Singapore. With hundreds of thousands of malwares released on a daily basis, these malicious programs are becoming more complex and hard to detect. However, if we are equipped with the right knowledge by knowing the most common types of malware and how to spot them, we’re a step closer to malware-proofing our company’s IT system.

Types of Malware
Worms
Computer worms are one of the most common types of malicious software. They cause harm to the host network by overloading web browsers and consuming bandwidth. Hence many companies require good IT services in Singapore to fix these issues. While this malicious program can be classified as virus, there are several characteristics that distinguish worms from regular computer viruses, such as its ability to independently self-replicate and spread over the network.
Virus
Like worms, computer viruses can also replicate and spread to other computers, but cannot activate until the user runs the infected file. Often attached in files, viruses are easily spread through emails and downloadable data from the Web. When activated, viruses can corrupt or delete data and sometimes can erase entire content of a hard disk.
Trojan Horse
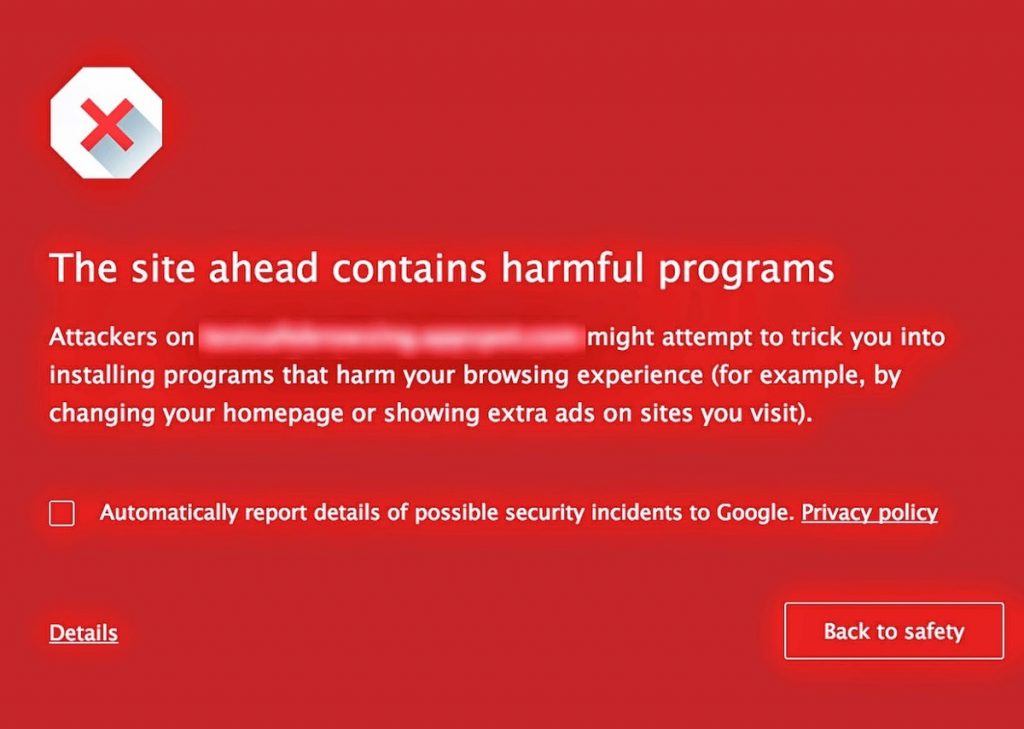
A Trojan horse, or commonly known as “Trojan,” is a destructive computer program that looks like a normal file to trick you into downloading and installing a malware. Attacks made by this malicious software can range from annoying pop-up ad windows to severe data theft and unauthorized system access. Unlike the first two malwares, Trojans do not self-replicate, but they penetrate the system the same way worms and viruses do—through Internet downloads and email attachments.
Bug
In the context of software, a bug is just a program flaw that produces undesired effects. These program flaws are usually the result of human error due to wrong source coding. Minor bugs slightly affect programs, while more significant bugs can cause a program to freeze or crash. Security bugs are the most alarming type of bugs as they allow hackers to override access privileges, bypass user authentication, and steal data. On the lighter note, however, bugs can be easily prevented with quality control, code analysis tools, and integration of IT services in the system.
Bot
Bots are programs created to automatically perform specific computer operations. Although some bots are created for harmless purposes, it is becoming increasingly common to encounter bots that function as malicious software. This malware can be used as spambots that pops up advertisements and as web spiders that wipes server data. Also, bots are utilized for distribution of malware disguised as popular search items and in botnets for DDoS attacks.
Actions You Can Do
Singapore business owners, especially those who own smaller businesses, often ask what they can do to protect important data and software from these harmful programs. The best place to start is to practice better and secure Web browsing and Internet practices. Web downloads and email attachments are seen as the easiest method for malwares to enter a system. Of course, using a good anti-virus software and enabling security firewall—along with keeping your operating system and computer programs updated—further helps in preventing penetration of majority of malwares into your IT infrastructure.
However, do remember that no system is 100% invincible to malicious programs. This is when professional IT services come as a big help. These experts ensure that your system is proactively monitored and managed to ensure healthy IT environment. Dedicated computer technicians and engineers make sure to maintain a secure IT interface through constant software update and anti-virus protection along with regular security analysis.


Leave a Reply
You must be logged in to post a comment.