Tech Wise
Apple iOS 10: 5 New Features to Watch Out For
On June 13, Apple introduced its newest operating system—the iOS 10—during the Worldwide Developer’s Conference (WWDC). Although the public beta is not yet available until July, we decided to download and try the developer preview version and threw together a list of five of the best features you can expect to arrive on your iPhone with the new iOS 10.

- “Raise to Wake” Lock Screen
One of the best additions to the newest iOS is your iPhone’s ability to wake itself when you raise it, fixing the common issue of blowing past the lockscreen notifications when hitting the Touch ID home button. Now, the new OS makes use of the internal sensors of the iPhone that enables your unit to light up whenever you raise your phone. A too-basic addition? Probably. But it’ll surely change your daily phone routine.
- No More Swipe to Unlock
Apple’s “Swipe to Unlock” feature has been the iPhone’s welcoming mat ever since the release of its first ever unit. Now, iOS 10 gets rid of this ancient feature and makes full use of the Touch ID button of the iPhone. To log into your phone, simply press the home button, which is activated by your fingerprint ID. If the home button is pressed by an unregistered fingerprint, you are prompted to punch in a passcode.
- Smarter Messaging App
iPhone’s Messaging app has taken its leap to dethrone Facebook Messenger and Snapchat through its tons of new features like text animations, handwritten notes, bigger emojis, animations that occupy the entire screen, and a whole lot of new apps for loading up standard messages with images, GIFs or whatever additions you can think of. It is a huge overhaul, so expect messaging getting into a whole new level.

- Interactive Notifications
Among the major visual changes in the new iOS is the notifications feature. On the previous OS, all you can do is dismiss notifications or launch it directly into the app. With iOS 10, you can respond directly to the notification or get more information about it. Press and hold the notification you wish to respond to, and bam—you’re good to go. The notifications themselves are also overhauled, appearing in frosted-like bubbles from simple Helvetica texts.
- “Delete” Stocked Apps
Finally, the long wait is over! Now, you can save more internal space by removing pre-installed iPhone apps that you do not use at all. However, Apple said that removing a built-in app doesn’t actually “deleting” it entirely; just removing user data, hooks, etc. Still, not bad—you get to free up some space for more relevant data that you can actually use.
These are just a few of the many new features to expect from the iOS 10. You get to experience these latest additions on your own handset through the public beta on July, and with the new iPhone 7 on September of this year.

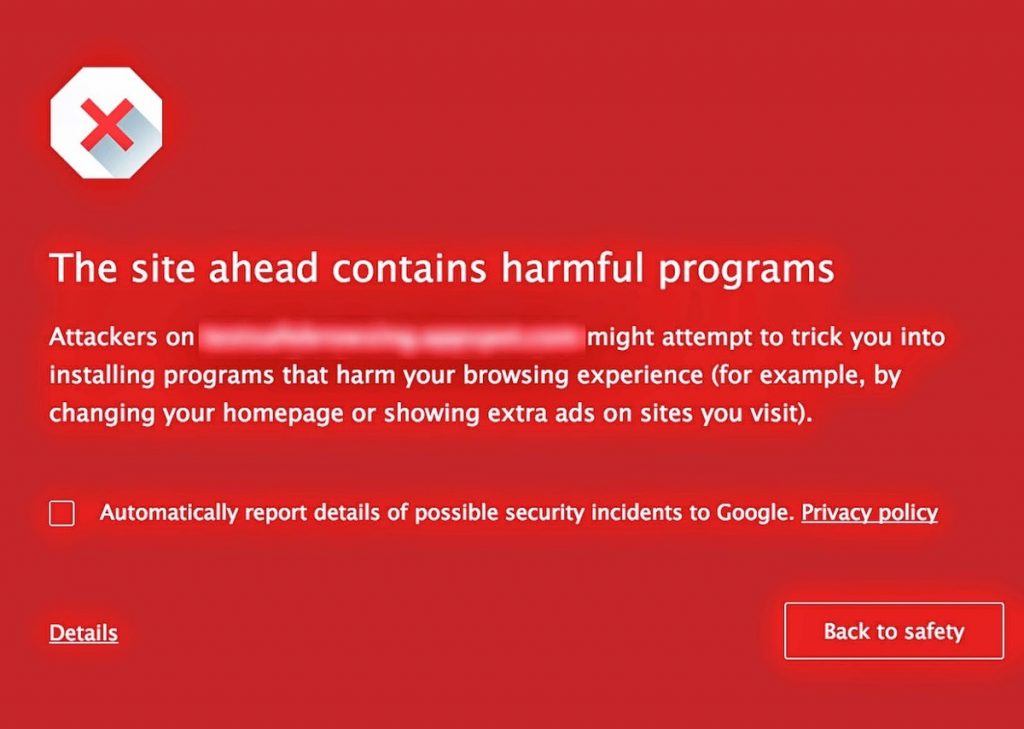
Cyber Security 101: Common Types of Malware
Cyber security is one of the constant issues that worries small to medium businesses in Singapore. With hundreds of thousands of malwares released on a daily basis, these malicious programs are becoming more complex and hard to detect. However, if we are equipped with the right knowledge by knowing the most common types of malware and how to spot them, we’re a step closer to malware-proofing our company’s IT system.

Types of Malware
Worms
Computer worms are one of the most common types of malicious software. They cause harm to the host network by overloading web browsers and consuming bandwidth. Hence many companies require good IT services in Singapore to fix these issues. While this malicious program can be classified as virus, there are several characteristics that distinguish worms from regular computer viruses, such as its ability to independently self-replicate and spread over the network.
Virus
Like worms, computer viruses can also replicate and spread to other computers, but cannot activate until the user runs the infected file. Often attached in files, viruses are easily spread through emails and downloadable data from the Web. When activated, viruses can corrupt or delete data and sometimes can erase entire content of a hard disk.
Trojan Horse
A Trojan horse, or commonly known as “Trojan,” is a destructive computer program that looks like a normal file to trick you into downloading and installing a malware. Attacks made by this malicious software can range from annoying pop-up ad windows to severe data theft and unauthorized system access. Unlike the first two malwares, Trojans do not self-replicate, but they penetrate the system the same way worms and viruses do—through Internet downloads and email attachments.
Bug
In the context of software, a bug is just a program flaw that produces undesired effects. These program flaws are usually the result of human error due to wrong source coding. Minor bugs slightly affect programs, while more significant bugs can cause a program to freeze or crash. Security bugs are the most alarming type of bugs as they allow hackers to override access privileges, bypass user authentication, and steal data. On the lighter note, however, bugs can be easily prevented with quality control, code analysis tools, and integration of IT services in the system.
Bot
Bots are programs created to automatically perform specific computer operations. Although some bots are created for harmless purposes, it is becoming increasingly common to encounter bots that function as malicious software. This malware can be used as spambots that pops up advertisements and as web spiders that wipes server data. Also, bots are utilized for distribution of malware disguised as popular search items and in botnets for DDoS attacks.
Actions You Can Do
Singapore business owners, especially those who own smaller businesses, often ask what they can do to protect important data and software from these harmful programs. The best place to start is to practice better and secure Web browsing and Internet practices. Web downloads and email attachments are seen as the easiest method for malwares to enter a system. Of course, using a good anti-virus software and enabling security firewall—along with keeping your operating system and computer programs updated—further helps in preventing penetration of majority of malwares into your IT infrastructure.
However, do remember that no system is 100% invincible to malicious programs. This is when professional IT services come as a big help. These experts ensure that your system is proactively monitored and managed to ensure healthy IT environment. Dedicated computer technicians and engineers make sure to maintain a secure IT interface through constant software update and anti-virus protection along with regular security analysis.

Age Guidelines for Electric Cars
I don’t have a kid yet but already I’m excited to buy toys for my future kids. On top of my list are electric cars. There are different and appropriate electric cars for every age group and I’ve already thought of which ones to get for my kid’s very first ride on car, when my kid turns three or four, when my kid is already big enough, and so on. I want to buy electric cars for my kids to give them a fun childhood memory as well as help them develop their motor skills.

Zero to Two Years Young
You’d want to get a small, light, and simple electric car for your kid’s very first ride on toy. Electric cars of this group are great for helping develop your child’s motor skills, hand-eye coordination, and balance.
Two to Four Years Young
This is when even parents start having fun in choosing what electric car to get for their kids. Electric cars of this group are larger, a little faster, and also come with more fun features.

Five to Seven Years Young
Parents may want to save more when their kids start reaching the age of five. This is when selection for electric cars of this group becomes more sophisticated that even adults can be envious. Realistic-looking cars of classic car models are available at this point. Parents may also want to get faster types of electric vehicles like go-karts and dune buggies.
Eight to Thirteen Years Young
I’m already planning on getting an electric ATV or electric dirt bike for my kid once he or she reaches eight years old. Maybe an electric dirt bike if it’s a boy and an electric scooter if it’s a girl. This is when electric vehicles at this point start to gain more power and speed. I also want to see my kids capable of riding on different types of vehicles.
Fourteen Years Young and Up
Teenagers at this point may start thinking of what to get for their very first real cars. I haven’t thought this far yet but my kids may still want to go on kart racing at this age so I’m thinking of getting a go-kart for my kid at this age. Even adults still go on kart racing and find it so much fun so I’m sure this will still be a hit among teenagers.

Introducing the Features of UOB Mighty
When you choose a bank, you consider its accessibility. If you already considered UOB, you have to know that it launched a mobile application that will let you make contactless payments with only your smartphone.

The application is called UOB Mighty. UOB is proud of the application’s different features which guarantee to make the lives of many Singaporeans fast and easy. You can manage your finances easily and accomplish daily banking needs instantly.
UOB Mighty features the following:
- View accounts: Since it can be accessed through your smartphone, you can view your UOB accounts anywhere and anytime you think necessary. The application can help you track how much money you have as well as how much money you owe.

- Transfer or pay: It is inconvenient waiting for your turn when paying bills, right? UOB Mighty can help with this dilemma because of its easy transfer or easy payment of bills. Steps are simple enough so there is no problem with the instructions. The good thing is that there are many establishments here in Singapore that is accredited and accepts transfer or pay.
- Book and share: Your UOB Mighty can also help you with booking and sharing a restaurant or a hotel room. The application is linked with your Facebook and other social platforms.
- Secured access: No one will consider it if it is not secured. UOB prides itself of secured access to prevent untoward things to happen.
Now that you know the features of UOB Mighty, it is time that you download it. Of course you need to join the bank first.
